Wondering how to secure your website? Don’t worry. We’ve got the perfect website security guide for 2021 for you to check out.
The Internet is full of malicious attacks and viruses that can take over your system and sites anytime. According to WebARX, 30,000 new websites are hacked and data is leaked daily on average.
With the rise in cyberattacks and data breaches, it’s more important now than ever to protect your site security.
To guide you on how to keep your site secure, we’ve prepared this simple definite website security guide for you.
What is Website Security? – Definition
Your website is basically a huge collection of your data and information. If your site is breached, then it can lead to various problems for your personal as well as corporate life. The hackers can misuse your data and cause different mishappening to your company, business, or your site.
Hence, without a doubt, website security is the most crucial thing in this time of constant cyberattacks and threats.

In simple terms, website security means keeping your website secure for yourself and your site users/visitors. It refers to the overall website protection techniques and measures implemented to secure a website.
Website security includes;
- detecting and solving security issues
- as well as preventing and responding to malicious attacks and threats.
In brief, site security is a set of rules and methods that helps you to implement different security measures to secure your site from security threats and cyberattacks.
Why Website Security is So Important? (Top 5 Reasons)
Website security is more important than ever before. It is one of the crucial things that you should always care about your site.
Wondering why? Here are some of the top reasons why site security is so important.
i) To protect customers’ and company data.
Your website holds numerous important data and information about your company, employees, or even your personal life. These are very critical information that you should protect from bad people.
If the hackers find this information by any means, then they can easily access more of your important information, passwords, credit cards detail, and misuse them. Also, they can violate the privacy of everyone associated with the company. Even worse, hackers can exploit customers’ data to target them directly.
Hackers are also able to access various confidential information of the company which can easily be leaked. They can also misuse such information to gain more profit. Worst of all, they can entirely shut down your site and get you out of business.
ii) Affects your site’s reputation and trust.
Having a secure site greatly affects how visitors perceive a site to be trustworthy and authentic. A company whose site is not secure loses reputation in the eye of consumers. This can cause the website to lose a huge number of traffic and loyal customers.
iii) To Protect Your Site from SEO Blacklisting.
You might have seen “This website might harm your computer” when you visit some websites. That is because the site is not secure and potentially contains malware.
Search engines aim to provide users with the most secure and reliable data. They are always working to show the best result to users. Because of the security issues in unsecured sites, search engines blacklist those websites and remove them from the list of potential search engine results.
These websites are shown with a warning page which causes many users to avoid it. As a result, 85% of online shoppers avoid insecure websites.
A secured site is regarded as reliable and trustworthy which helps gather more traffic fast. And it is exactly the opposite of an unsecured site. So, having a secured site is important for the site to grow fast and avoid common web security threats.
iv) To stop diverting traffic and crashing your site.
The Internet is full of viruses and malware that help hackers get into the websites. If your site is not secure enough, then they can easily hack your site as well.
Once your site is infiltrated, then the full control lies in the hands of hackers. They can easily divert your traffic to different websites, publish unwanted content, or even shut down your site.
v) The number of Websites hacked is rising rapidly.
The average number of website attacks is increasing every year. A study shows that there is one hacker attack every 39 seconds and about 43% of hacks are targeted towards small businesses. If hacked once, small businesses can hardly get back to their feet easily.
Although attacks don’t always mean successful hacks, staying alert, and using security measures is very crucial.
How do Websites Get Hacked? (10 Major Ways)
With time, hackers and attackers have advanced their techniques of attacking and infiltrating a system. There are many different ways a website can get hacked. It is virtually impossible to keep track of every way and avoid them.
But there are some common methods that hackers follow to break into a website. Let’s talk about major ways websites get hacked.
1. DoS/DDoS Attack
Denial of service (DoS) attacks are done by hackers to tie up the resources of the site. This attack restricts users from accessing the site. A single internet protocol (IP) or system launches the attack which floods the site with a huge number of fake traffic making its resources inaccessible to general users.
Although effective in its time, many systems and sites can easily overcome the DoS attack today. DoS attack has evolved into a more sophisticated attack called distributed denial of service (DDoS) attack. They attack a site using a large number of infected devices called botnets.
For example, if you are getting an unnatural amount of traffic on your site, then you might be in the middle of a DDoS attack. Attackers can flood your site with the help of these botnets then use the vulnerability and time loss while getting back online to exploit and get full control over your site.
2. Malware and Virus
Malware, short for malicious software, and viruses are the most common and widely used ways to hack websites. People are bound to come across various sites and ads and suspicious websites that might transmit malware. Malware enables the hacker to launch other different attacks.
They can easily use your site’s resources, gain access to confidential information, and also your site visitors’ systems. This puts the privacy and information of the company and visitors associated with the site at a huge risk.
If secure comment filtering is not available for your site, hackers can comment on malicious code that can easily get into the system. They can use malware as a gateway to your site and take full control.
3. XSS Attack
Cross-Site Scripting (XSS) attacks are a type of injection attack. Hackers and attackers inject malicious code into a trustful website using web applications. These malicious codes are generally in the form of browser-side script which is not detected as any kind of attack by a system.
Hackers can inject your site with malicious codes that the browsers run. This will allow hackers to hijack sensitive data and cookies stored in the web application. The attack can also change the content of the HTML or redirect users to a different page.
4. SQL Injection
Structured Query Language (SQL) injection is one of the most common code injection attacks which directly targets the database of a site and has the potential to destroy it. Attackers inject SQL commands to the data-plane input and the site executes it.
If your website allows users to search for products or access some part of the database, then that is where SQLi is more probable. For example, hackers can input certain bits of code to force execute different commands to access confidential data. This code is called malicious payload.
Hackers input this malicious payload in your site search input box. And, with correct code and command, the attacker can interfere with the queries of the database and view sensitive data stored in the database. This can help attackers retrieve different information for further exploitation and attacks.
5. Access control
Gaining access to the website’s admin area or server can easily compromise a website. If a hacker is able to get past the authentication and authorization part, then they can completely access your site’s control.
In particular, if a hacker is able to guess your login credential by use of social engineering or software, then they can get hold of various confidential information. They can easily gain control over your site.
Attackers basically own your site if they gain control. They will be able to leak confidential data, use it for further hacks, and more. Hackers deploy various different new ways to get access control for sites. But the most common form is a brute force attack.
6. Transport Layer Exploits
The transfer of data between websites and web servers may include different confidential and important information. They frequently transmit data like authentication details, credit card details, login details, and more.
For example, if attackers can exploit the transport layer vulnerability, then they can trick the site users and redirect them to a malicious site. The hackers can access the confidential data and retrieve information even if it is encrypted.
Attackers can commence different attacks like Man-in-the-middle (MITM) attack to retrieve the decrypt key if they pinpoint the vulnerability in the transport layer. They can now access the encrypted data from the site and decrypt using the key.
7. Using Insecure web hosting
Web hosting is very important for the security of a website. Different web hosting services have good security against various types of issues like DDoS protection, SSL encryption, etc. But not all hosting companies take security measures equally, so you must choose a web hosting carefully.
Using insecure web hosting can also increase chances of data leaks which can result in making your site vulnerable. If your hosting is not secure enough, then hackers can gain access to your site.
For example, hackers can get into insecure web hosting platform’s databases by various types of attack. This will leave all the websites’ data associated with the platform vulnerable. They can use those data to easily deploy basic security attacks to your site.
8. Usage of weak passwords
If a hacker or attacker is able to access your username and password, then they can easily take control of your site. The usage of weak passwords makes your site very vulnerable to attackers and their brute force attacks.
For example, hackers can use various kinds of software or social engineering to brute force their way to your password. Weak passwords make the job easy for hackers and they get into your site using credentials in no time.
Using password managers can help to generate strong passwords and keep them safe. Therefore, it’s very important to have secure login details to avoid them from guessing or easily cracking your password.
9. Software Vulnerabilities
Some software sometimes can have bugs and loopholes unknown to the developer. Hackers are very proficient in exploiting bugs in software for their benefits. These security issues in software cause the system to be very vulnerable to attacks and exploitation.
For example, a particular software might be vulnerable to certain malware. If you use that particular software, hackers can exploit the vulnerability to get into your site.
Consequently, attackers are able to deploy many attacks like Remote File Inclusion (RFI), SQL injection, Local File Inclusion (LFI), and more. These attacks help attackers take full control of the site.
10. Third-party integration
Third-party integration is a very common thing for websites. For example, you may do third-party integration to monetize via ads. But this can make your site very vulnerable from the security perspective.
These third-party integrations are given much more control of the site for better functioning. But they are prone to get infected too. If the hackers are successful in infecting these integrations with malware and virus, then they can also hack into your site easily.
For instance, hackers can get into an insecure extension and infect it with dangerous malware. If you add those extensions to your site, then the malware can easily take over the site and give authority to the hacker.
What are Common Website Security Threats?
There are many security threats that you have to be cautious of. Some might hack into your site and system to gain control whereas some might get hold of your information or data. It is very important to be aware of common security threats that are often overlooked by general people.
1. Spam
Spam is unwanted and unsolicited messages or comments that are sent out in bulk. Your website is bound to get multiple amounts of spams the more it grows. Hackers integrate malicious content in the form of URLs in those spams. Anyone who clicks and follows through the spam URL becomes vulnerable to those attackers.
It is very important to check for spam in your site and control them to protect your business and customers’ data.
2. WHOIS domain registration
When you are getting a domain for your site, you are required to release some information about yourself or your company. This is recorded on the WHOIS data. This information contains your personal details and your website details.
Hackers can get hold of this information and use it to exploit your sites or leak them to the public that can cause further problems and issues.
3. Defacement
Defacement is an attack where the attackers exploit vulnerabilities in a site and replace your site’s content with malicious content. When visitors get into your site, they are displayed various malicious content at the top of your site.
This can gravely affect your reputation as a company. These attacks are mostly done by attackers and defacers to spread hate messages or different views on controversial topics.
4. Pharming
Pharming is an attack that redirects a site’s traffic to a fake site to get confidential information out of them. The attackers mostly change the host file in the victim’s computer by deploying malware and targets the victim’s credit card details, passwords, and other details.
In the attack, the victim is redirected to an identical fake site and asks for their credentials. Many victims, unknown to the attack, give away their confidential information which makes them vulnerable to further attacks.
5. Ransomware
Ransomware is a malware attack that attacks visitors in different ways. They sneak into the system and restrict access or change file content. Then as the name suggests, ask a ransom fee in exchange for solving their PC issues.
The attackers often choose the comment section of a site as their malware spamming ground. It is very important as a user to be cautious of what link they visit and as a site owner to have proper protection for it.
6. CSRF attack
Cross-site request forgery (CSRF) is a web vulnerability that allows the attacker to deceive users to perform actions that they don’t intend to. Attackers send a malicious request to a web application from authenticated users. Like in ransomware, attackers spam malicious links and infect users.
Now, when the infected but authentic users send a request to a website or web app, the attackers intervene with the CSRF attack and change the request to malicious request.
7. Accidental file deletion
Although not a hacker attack, accidental file deletion is one of the most common security threats website admins often fall into.
Running a website requires clusters of files and folders containing your site’s content and information. What if you accidentally delete them? Your website will be gone!
This accidental deletion of files can come off as a huge threat with no proper solution. But with precautions like backups can save your life by letting you restore your site.
8. SEO blacklist
Search engines are optimized to display the most secure and relevant sites on the top of their result pages. So, if a site has bad security history then it is blacklisted by search engines. Such a phenomenon is called SEO blacklisting.
This is actually not a security threat but a warning from search engines to you. If your site is blacklisted, then search engines will stop your content from appearing on their result pages. Consequently, you’ll lose all the organic traffic.
Hackers also attack sites to decrease the ranking of direct rival sites in the search results.
9. Security Misconfiguration
Security misconfiguration is another very common threat to your website security. A website uses different systems and applications with their own security configurations. For example, hosting servers, website software, plugins, and applications.
If the configuration is not proper, then it would open various vulnerabilities for the hackers to exploit and get into your site.
How to Secure a Website? (15 Best Tips to Protect Your Site)
As you already know, there are several kinds of security attacks that have the potential to spoil your site and shut down your business entirely.
But you can keep those threats in check and avoid attacks if you implement some security measures on your website. Following these security practices not only keep your website secure but also help to keep your brand’s credibility strong among your users.
We strongly recommend you to implement these measures on your site. Let’s check them out.
1. Install SSL certificates
The first thing you should do is get a Secure Sockets Layer (SSL) certificate for your site.
SSL is the standard technology to transmit data safely between the web server and the browser. This ensures that information passed between the users and your site is encrypted (private) and safe.
For example, your site users may enter information like emails, credit card details, etc. This information will be transferred to the webserver after they submit it. SSL protects that process by encrypting.
You can get an SSL certificate from your domain registrar or from other SSL provider companies. Some companies like Let’s Encrypt provide SSL for free.
To know whether your site already has an SSL, you can simply check its URL. If it starts with ‘https://’, then it’s SSL certified. If it has only ‘http://’ without ‘s’, then you should quickly get it.
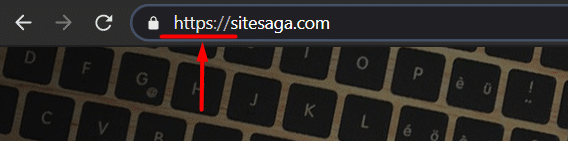
Using SSL is even more important nowadays because the latest browsers like Google Chrome show ‘not secure’ for non-SSL sites.
2. Use Strong and Secure Passwords
One of the most common methods that hackers use to get hold of your website is by brute-forcing and guessing your password. Attackers use a number of methods and social engineering to gather information on you to gain credentials.
To avoid that, it is very important to have a secure and strong password for your site login. You shouldn’t use passwords that are easy to guess and go for something that is secure.
We suggest you not to use a password like a birthday, name and phone number. They are often very easy to guess and give away your security. You should include a mixture of random capital letters, small letters, numbers, and special characters to make your password strong and secure.
People have a tendency to use the same password on multiple platforms. This increases the chances of attacks tremendously. So, it is very important to have a strong and secure password for each different platform.
We know that generating and remembering those complex passwords for each new site can be a great hassle. But you don’t have to worry about that.

You can use various trustworthy password managers like LastPass, Zoho Vault, etc. which generates new and secure passwords for each website. They can also save those passwords for you so you won’t have to remember them. The only password you have to remember is the master password associated with those password managers and leave other passwords to them.
3. Knowledge and implementation of CIA triad
CIA triad – Confidentiality, Integrity, and Availability triangle is a very common model that is used to develop policies for security. These are the basic model of security and proper implementation of this can increase website security.
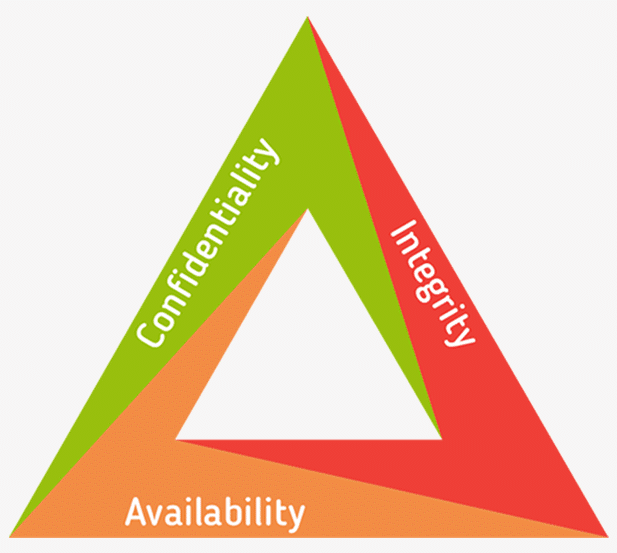
Confidentiality refers to who should have access to confidential information. It can be for login credentials and other secret information.
Integrity refers to the accurate, credible, and unbiased information that is provided to the consumers. It overlooks if any alteration occurs during the transfer of information to the users. It implements the SSL encryption to secure the data transfer.
Lastly, Availability means if the data is accessible when needed. The attacks like DDoS are the major threat to availability.
The proper knowledge about this CIA triad helps the organization ensure good security to their website and protect their confidential data.
4. Regular update of website platform and software
Most website platforms like WordPress, Joomla, etc. provide frequent updates with security fixes. They release new software versions to fix and stop the security issues found in their earlier versions.

So, you must always keep an eye on the new updates offered by the website platform you’re using and implement the updates immediately on your site.
Some software companies even hire people to attack their own software to find vulnerabilities. They try to track the loopholes and fix them all before any bad person takes advantage of them.
The bottom line, you should always use the latest version of any website software.
5. Properly configure the CMS settings for Better Security
When you’re installing a Content Management System (CMS) of your choice, the security settings are already set to default by the system. This can save some time while starting with your website but this opens a huge security vulnerability.
Many hackers specifically develop automated attacks to target websites with default CMS settings. There are many users who don’t pay attention to changing the default CMS settings which can help attackers achieve their goal of targeting a wide range of websites.
For example, if your website platform by default allows all comments without requiring approval, then hackers can use that to post malicious links on your site. Simply changing that setting can save your site from being hacked.
Similarly, there can be settings like file permissions, user control, etc. which you need to configure properly as soon as you set up your site. This will help you avoid a large number of attacks and implement good website security.
6. Cautious Selection of Third-Party Plugins and Extensions
Many CMS allows users to extend the functionality of their site by adding third-party extensions. For example, you can add any kind of feature with the help of plugins to your WordPress site. Similarly, other CMS platforms also provide such capabilities.
When you add those extensions, the extensions are allowed into your site to add features. But, extending the feature of your site using third-party extensions comes with a huge security risk. All the third-party extensions can’t be trusted in terms of security. They might come with malware preinstalled or have security issues.
Hackers can use those third-party extensions and embed malware into them to attack a huge number of sites and gain access.
So, you have to be cautious while choosing such plugins and extensions. We suggest you get those extensions from trusted providers. It is also very important to check for their update frequency and their history on security issues before adding them to your site.
For example, if you’re using WordPress, then it’s best to get plugins from the official plugin repository at WordPress.org. The plugins listed there are strictly checked for security. Also, you can see last updated date, user reviews, ratings, number of downloads, etc. to see how the plugin actually is.
For more details, you can check our full guide on how to choose the best WordPress plugins.
7. Use Powerful Security Tools and Plugins
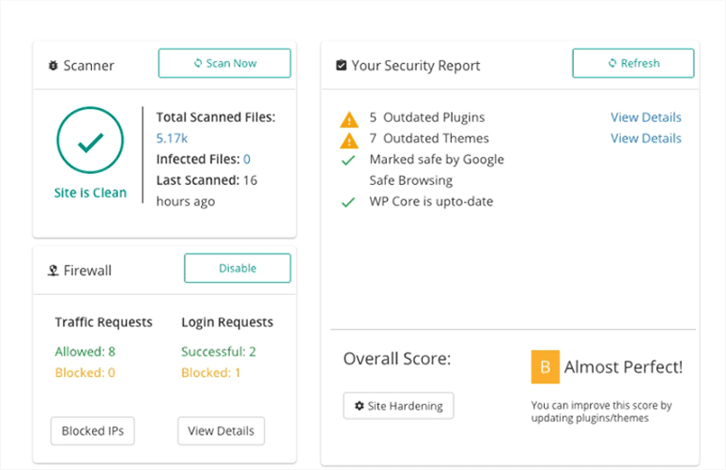
One easy way to strengthen your site’s security is by using security tools. Such tools harden your site’s security, scan your site to check vulnerabilities, monitor suspicious activities, and stop common security attacks. Different CMS also provides those security tools in the form of extensions to your site like plugins.
There are plenty of website security tools and plugins available on the market. Some of them provide overall security features while some are specifically focused on certain features like scanning, malware removal, firewall, backup, etc.
For example, Sucuri Security is a popular website security solution that provides many different features like malware scan and removal, DDoS mitigation, SSL, etc.

Also, you can find platform-specific plugins as well. For example, there are plugins like iThemes Security, Wordfence, etc. for the WordPress platform. If you’re using WordPress by chance, then you’re in luck because many of the popular WordPress security plugins are available for free.
8. Use Web Application Firewall
A firewall protects your system from any unauthorized access. They also constantly filter any incoming request and protect your system from common security attacks like DDoS and malware.
Similarly, Web Application Firewall (WAF) analyzes your website’s traffic for any suspicious activity. Vulnerability in your web application can allow attackers with great pathways into your site. This is where WAF is crucial as it protects your web application from different attacks.
Implementation of WAF helps you monitor dangerous threats like DDoS attacks, CSRF attacks, XSS, and SQL injection. Although it’s not the absolute defense against cyberattacks, they stop a wide range of automated attacks and keep your site secure.
Some of the best website firewall providers are Sucuri, Cloudflare, and SiteLock.
9. Use Two-factor Authentication for Login
Two-factor authentication is a very secure way to fight against unauthorized login attempts. It requires anyone to complete 2 authentication factors to log into your site.
Normally, you may use one password to access your site’s admin area, but two-factor authentication lets you add one more factor for logging into your site.
The second authentication factor can be a passcode sent to you via SMS, email, or via authenticator apps. Modern interactive applications even use biometric factors such as fingerprint and facial scan.
If you’ve added two-factor authentication on your site’s login, then you will get a notification every time a login attempt is made. So, you’ll know about the unauthorized login attempts immediately and you can report/block such attempts.
This also protects your site from hackers who are trying to hack into your site by guessing passwords because you’ll have to approve every login with the second factor.
10. Frequent Scanning and Monitoring of Vulnerabilities
Attackers can leave malicious code to your site via comment or mail. There is a high chance that it can open vulnerability in your website. You have to be cautious of suspicious activities to protect your site from security threats.
It is important to frequently look for vulnerabilities in your website to strengthen your site’s security. Frequent scanning and monitoring of your site for any vulnerability, malware, and suspicious activity can help you take preventive measures against common attacks.
This can be achieved by using different security check tools and also extensions provided for different CMS life security check plugins for WordPress.
Using these check tools is the best method to constantly check the status of your site and its security. They will highlight your website’s weak points and enable you to solve them accordingly.
11. Create Regular Backups
Having a proper backup of your website’s data is very important. There is a high chance that hackers will delete your data and content from your site if they infiltrate. In a situation like this, your site will be nothing more than just a URL link.
This can cause a huge loss in organic traffic and a backlash in your reputation. Recovering those lost data and getting back to the previous pace can take a lot of time and effort. Therefore, it is very important to prepare for this situation.
There are a number of backup options that you can use to store your data as a precaution. Many CMS also provided platform-specific backup extensions. For example, you can use plugins like UpdraftPlus, BackupBuddy, and VaultPress for creating backups in WordPress.
Next to that, hosting providers also include backup features with their web hosting services sometimes. Or you can also manually create backups and store in your local computer or cloud locations like Google Drive or Dropbox.
Having a proper backup service can help you mitigate the problem and risk of data loss. The regular backup will help you overcome any unfortunate time if your site data is deleted.
12. Choose a Secure Web hosting Service
Web hosting service is equally important in keeping your site secure. A vulnerable hosting platform and service can automatically put the sites at risk.
Your site security can depend a lot on what plan you choose to go with. Many web hosting plans have a secure hosting server which guards against cyberattacks. But that’s not always the case. Hosting providers offer different types of services for different price ranges.
Among them, shared hosting might seem tempting because of its pricing. But it is not the most secure option. You share the server for your hosting with other websites in this plan and this increases the security risk.
If one site is hacked and the hackers infiltrate the server, then all the other sites are put into risk. This makes your site more prone to cross-site contamination. Attackers can now easily attack your site.
Choosing a safe and secure web hosting service can eliminate those risks. Going for a tab bit expensive but very secure option can increase your website security by a lot.
Some of the most secure web hosting services are SiteGround, Bluehost, and HostGator.
13. Properly Manage Your Website Server
Your website server is what holds every aspect of your website together. It is the most crucial factor in running a website. However, it is also the target of many attackers and hackers.
You have to be cautious of the security settings and measures that are applied to secure your server.
Frequently going over the security settings, monitoring the server and proper management of the server is very important to keep the attackers at bay.
14. Hash and Encrypt your Website Stored Data
All the confidential data that is entered by the users like credit card details, password, social security number, etc. are stored by your website. Because of its confidentiality and importance, it is your responsibility to keep it secure.
These data are stored in an application database. Hashing changes these data into an unreadable combination of code that can not be reversed. Whereas encryption changes the content of the file and will require a specific key to decrypt it to a readable state.
Hashing and encrypting will ensure the inability of hackers to gain information from the stored data even if they are successful in infiltrating your site. This will prevent the leakage of data and secure confidential information.
15. WHOIS protection
One common way of getting information about your site is through the WHOIS database. WHOIS database contains your details like name, email, number, address, and domain registration information.
The collected data is basically the information that you provide to the domain registrar while getting your domain. The domain registrar then passes this data to the International Corporation of Assigned Names and Numbers (ICANN) which is then added to the WHOIS database.
These data are publicly accessible from the WHOIS database unless you subscribe to WHOIS protection. Most of the domain registrars provide WHOIS protection for a little extra payment. Whereas some companies like NameCheap have free options like WhoisGuard.
WHOIS protection helps shield your data from anyone looking up your information in WHOIS lookup. It displays the details of the registrar instead of your details which protects your data from getting into the wrong hands.
5 Free Website Security Check Tools
It is important to frequently monitor and check for any security vulnerabilities in your website. You have to be aware of any weak points in your site and update it constantly to keep it secure.
Fortunately, there are plenty of online tools that let you test your site’s security free of cost. Here, we’ll show you some of the best free website security check tools.
1. Sucuri SiteChecker
Sucuri SiteChecker is one of the most popular free website security check tools.
You can head onto the Sucuri SiteChecker website here. You can now enter the website URL that you want to scan.
Sucuri will check your website for all known malware. As it’s not scanning your server file but just the front-end of your site, it is only able to scan for the malware in the front-end of the site.
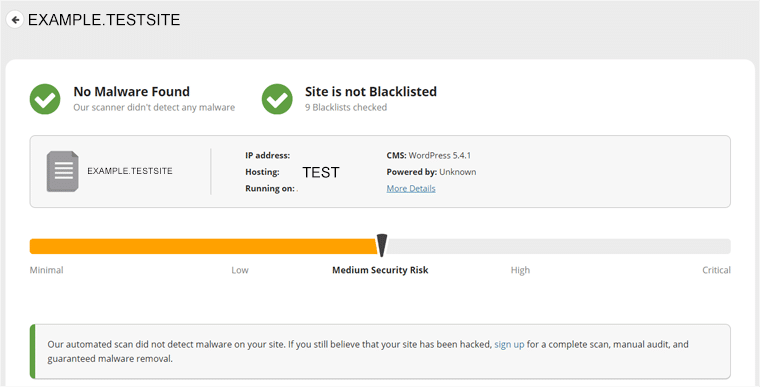
It will also look for any viruses, website errors, out-of-date software, and malicious code present in your website. It shows the report in a simple interface along with an estimated risk gauge and some recommendations you can apply to strengthen your site security. You can also check the blacklist and SSL status.
Sucuri SiteChecker is totally free and you can easily go to the site to check the security of your site. It also has a free plugin that you can integrate into the WordPress site for free security scans.
2. MalCare
MalCare is one of the best malware scanner tools for your WordPress site. Along with its website vulnerability scanner, it also provides cleanup and protection measures. MalCare can detect new and complex malware and give accurate information.
You’ve to sign up for a MalCare account from the website. Then you can add the MalCare plugins for WordPress from the site. This will allow you to easily use the MalCare plugin to scan your site for any malware and security threats. It provides a thorough report of the threats and malware if found.
Unlike some malware scanners, MalCare doesn’t affect the speed of the site. It runs the scan in its own web server. This decreases the consumption of resources of your server and doesn’t slow down your site.
MalCare runs a scheduled scan every day. You won’t need to configure anything and it will automatically start. And, you are not restricted with only that, scans can be done at any point in time when you require.
3. Observatory
Observatory, by Mozilla, is a free website security checker tool. It is a very detailed security check that also integrates checks from third-party platforms. It has some learning curve to understand how it works.
You can just visit the site and initiate a scan with no hassle or log in. It divides your scan result to 4 sections:
- HTTP Observatory
- TLS Observatory
- SSH Observatory
- Third-party Tests
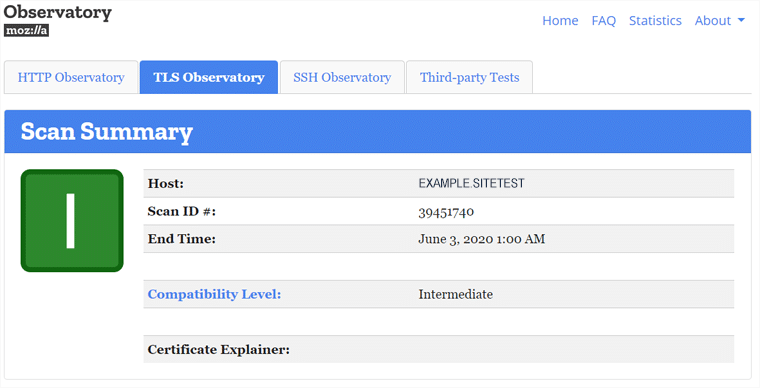
Observatory also checks your site against multiple third-party tools like SSL Labs, Security Headers, and HSTS Preload and displays the result. It checks for the existence of SSL certificates and other security measures. It also checks how the implementation is.
4. UPGuard Web Scan
UPGuard Web Scan is one of the most popular website security check tools that checks your site against a number of parameters. It checks your site thoroughly to scan for any malware or if it is hacked.
You can go to the site and enter the URL of the site that you want to scan. It implements the rating system of the site security from 0 – 950. It performs security checks for website risk, email security, network security, and malware along with brand protection.
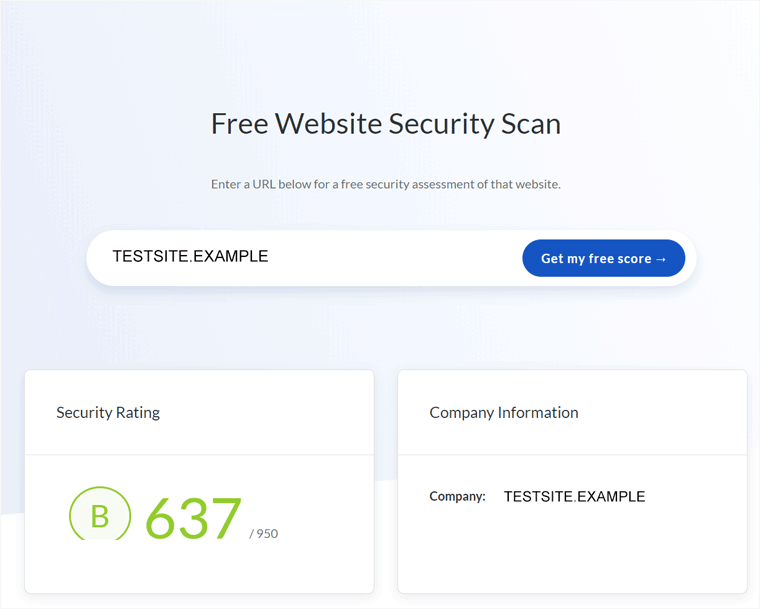
UPGuard also predicts and detects hacks that are susceptible to your site. Although it lacks the ability to detect complex and new malware, it provides a good detection rate for normal malware.
5. SSLTrust
SSLTrust is a great security check tool that is more than just an SSL certificate checker. It checks your website security with other trustful third-party tools like OpenPhish, Google Safe Browsing, Sucuri SiteChecker, etc.
You will be able to enter the URL of the site that you want to scan when you visit the site. Although it checks with a huge number of services, it only shows if the site is secure, insecure, or unrated.
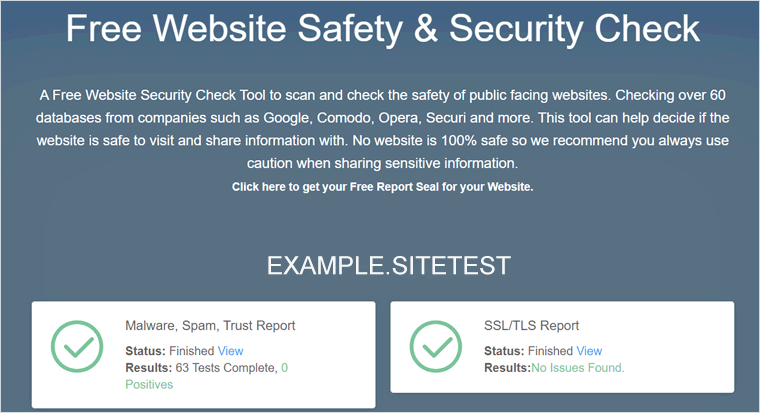
Except for the SSL/TLS status, it doesn’t dive deep into different issues or solutions and it only detects the existing issues.
Conclusion
Visitor interaction is important to increase the traffic on your site. But to maintain a good reputation with your visitors and make them feel secure, it is important to implement website security. This provides your customers with a sense of security and builds more trust.
Website security plays the most vital role in running a successful and secure website. You have to be cautious of the rules and tips to keep your website secure and avoid any cyberthreats.
One of the most basic security steps is to have a secure web hosting service. You also have to implement a firewall on the server-side of your site as well as WAF. Then you can go about completing the security blocks to protect your site from any kind of security issue.
It is also important to frequently check for updates of your platform and have a good security check tool. There are many other tips that you have to follow to protect your site and you can go about them one at a time.
We hope this guide helped you to understand what website security is, what are the major security threats, and how to protect your site from such threats. If you have any further questions about site security, then leave a comment below. We’ll try to get back to you as soon as possible.
Check out our article on Website Speed 101 for a complete guide on enhancing your site’s speed.